On April 7th, 2014, a serious security vulnerability was publicly announced in the popular OpenSSL software library, which is used by many web systems for encrypting and decrypting data. The bug opens up the secret keys used to identify the service providers and to encrypt the traffic, the names and passwords of the users and the actual content. If exploited, attackers could eavesdrop on communications, steal data directly from the services and users and to impersonate services and users.
PCRecruiter software runs on web servers which do not use the OpenSSL library by default and therefore are not vulnerable to the exploit.
If you are a PCRecruiter user concerened that your password may have been compromised by use with another website, you may wish to use the 'Change My Password' option on the MyPCR screen to update your password. It's a 'best practice' to change passwords regularly.
Your PCRecruiter system administrator may also select a strong password mode. In this mode:
For more information on security practices in PCRecruiter, contact your representative.
For more information on the Heartbleed bug, see http://www.heartbleed.com/

“X-ray search” has been a secret super-power to sourcing heroes for a while now. However, some recent changes have made it more challenging to use effectively. Today, let’s discuss what X-ray search is and what seems to be happening to it.
Read more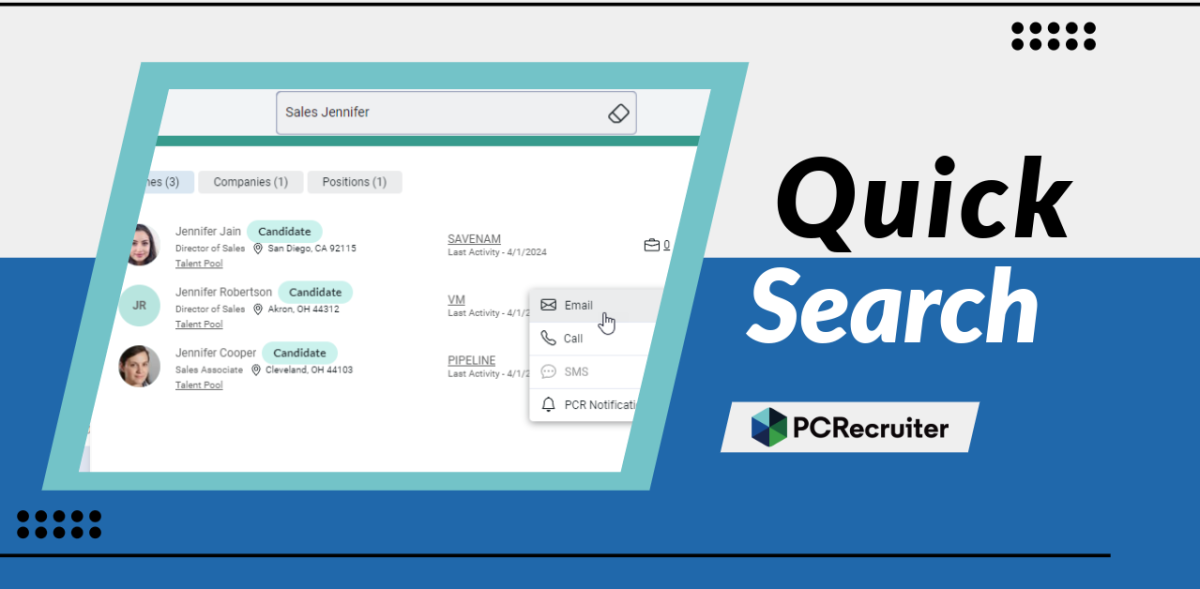
The PCRecruiter system has been updated today, and the most noticeable change you’ll find is the replacement of our ‘Quick Find’ feature with a new ‘Quick Search’. This search box appears in the upper right hand corner of the PCR screen.
Read more
When choosing a database or other data processing vendor, safeguarding your organization’s information and experiencing consistent application uptime are fundamental, but making informed decisions can be challenging.
Read moreFind out more about who we and what we do.