When it comes to data security, all recruiters need the right level of training and awareness. But the right applicant tracking system (ATS) should be able to handle data security, freeing up recruitment professionals to focus on their core business.
Your applicant tracking system (ATS) is the gateway to a goldmine of personal and enterprise data. And with recent and ongoing developments in data privacy regulations, such as General Data Protection Regulation (GDPR), a data breach can be costly, inflicting irreparable damage to your client’s and candidate’s trust and your company’s reputation.
Whether your sensitive data is held in a public cloud, private cloud, or on premises, recruitment firms and HR professionals have an obligation to ensure data security and compliance with data privacy law and regulations. So how can you protect company, client, and candidate data from the threat of cyberattacks, unauthorized access, or even accidental exposure?
Let’s take a closer look at data security in recruitment, and how you can mitigate the risk by taking the right preventative measures.
What is data security?
Data security involves protecting digital information from corruption and unauthorized access wherever it resides, in transit, at rest, or at the end of its lifecycle when it’s no longer required. Digital data security can be enacted in a number of ways, including encryption, masking, and tokenization. It also requires additional measures to mitigate data breaches, including backup copies and secure storage.
Why is data security important?
Research shows that in 2020 there were nearly 30,000 cybersecurity incidents worldwide, with 3,236 in the public sector and 2,935 in the information industry. In the same year, there were over 300 million reported ransomware attacks – where attackers threaten to permanently prevent access to a victim’s data unless a ransom is paid.
Unsurprisingly, two of the most targeted file types are database file extensions (like .db) and SQL (Structured Query Language) which is the standard language for manipulating database, and relational database management systems. Both of these file types are commonly used by every type of recruitment professional, from recruitment agencies to HR departments. But with the right ATS in place, there’s no undue cause for alarm.
What are the different types of data security?
Organizations of every size have a raft of data security measures at their disposal. The right security solution, as part of a wider internal security strategy, will take account of the risk, compliance regulations, and sensitivity of specific datasets to deploy the right level of security control. This helps to mitigate the risks in data handling and storage.
Recruitment is one example of an industry that deals with a constant flow of incoming and outgoing flow of personal and organizational data. And like other industries, there are common data security measures that can be put in place for reducing risk and avoiding a breach. These include:
- Encryption
- Backups and recovery
- Secure storage
- Authentication
- Access controls
An ATS that’s compliant and secure
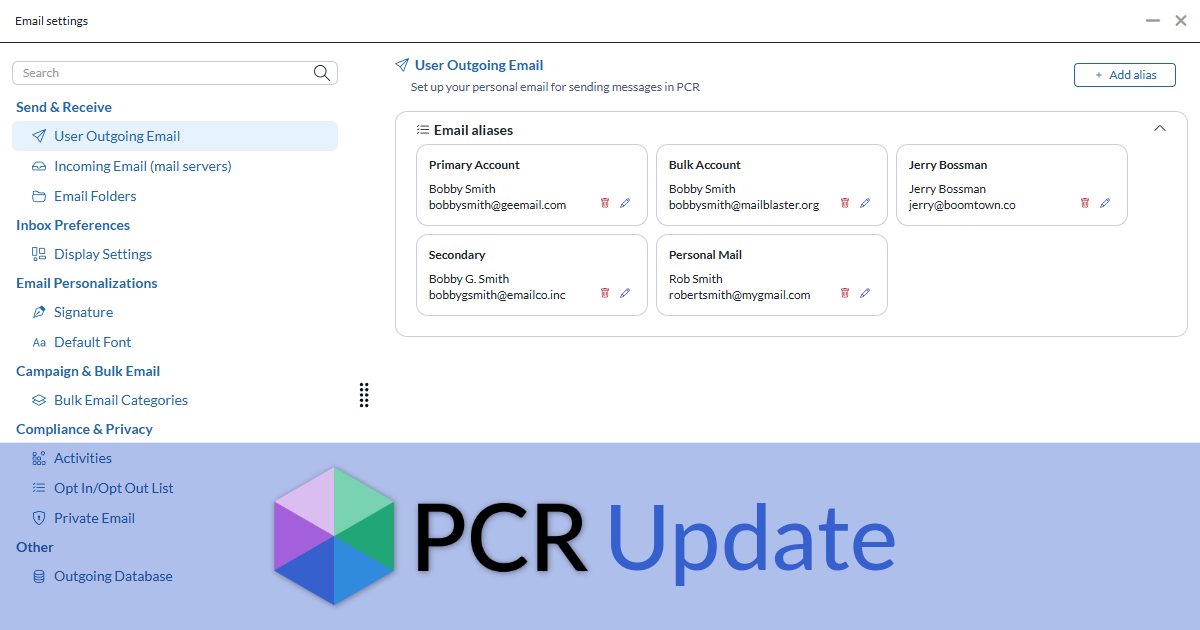
As a provider of recruitment CRM / ATS hybrid, CLICK HERE TO LEARN MORE handles large volumes of sensitive data every day – between 8,000 and 9,000 separate databases ranging from 100MB to 7TB in size. So for us, data security is business critical and a core part of what we do.
Our ISO certified data center has a rigorous security process for entry, 24/7 staffing and caged equipment. Whilst we can offer bespoke levels of security encryption (including asymmetrical encryption for organizations who wish to encrypt their own data) all of our data undergoes industry standard encryption. And anything leaving one of our data centers is automatically encrypted, such as quarterly backups, which are removed and stored securely in a vault. Plus, we back up to two separate geographic locations in case of a natural disaster or security incident in one location.
Our software is regularly scheduled for pen testing (ethical hacking) to evaluate the robustness of its security features. In addition, developers go through extensive training in data security. For third-party developers wishing to utilize our application programming interface (API), we provide access tokens which restrict access to specific functionality.
Alongside these security measures, we offer opt-in security settings for recruiters. These include the following Two-Factor Authentication (2FA) settings:
- Invalid password lock out
- Email authentication
- TOPTP (time-based one-time password)
Peace of mind with PCRecruiter
Since 1997, Main Sequence – the company behind PCRecruiter – has built a strong reputation for being one of the world’s most trusted and successful developers of recruitment, sourcing, and applicant tracking software. PCRecruiter is a software as a service (SaaS) built on its own operating system and platform with cybersecurity baked in. It provides thousands of recruiters around the world with data security they both need and trust.
Find out more about our commitment to the highest standards in data protection and adherence to compliance regulations in our blog post PCRecruiter is ready for the GDPR.